What is Vulnerability Assessment ?
Our Hybrid methodology uses OWASP Top 10 methodology along with manual testing which uncovers wide range of business logic Vulnerabilities. The market is brimming with large number of tools that address any issue and an appropriately checked vulnerability scan can uncover a ton about a domain.What a vulnerability scan cannot do, is exploit those weaknesses to prove their severity or determine the extent the control environment’s potential for compromise. Here comes our manual testing approach where the vulnerabilities are been exploited, which give a cutting edge results.
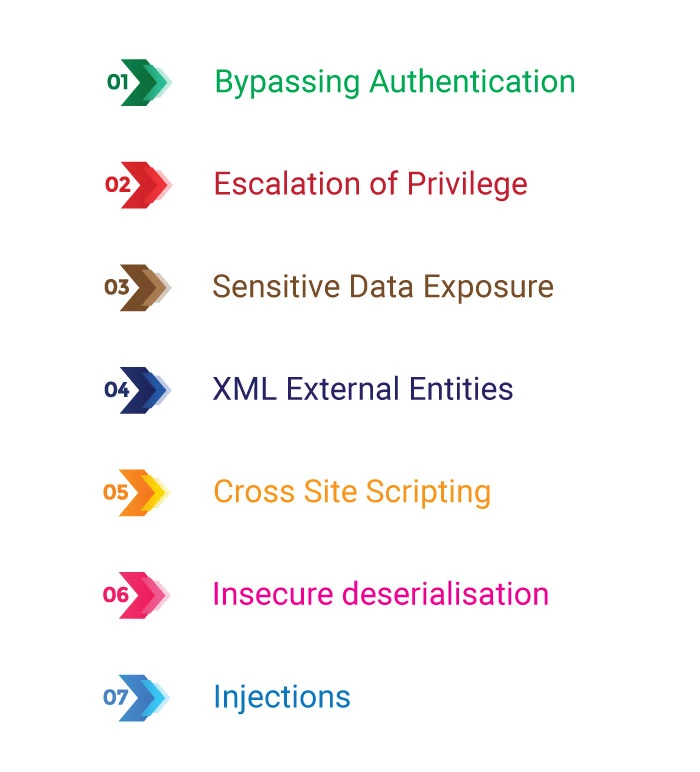
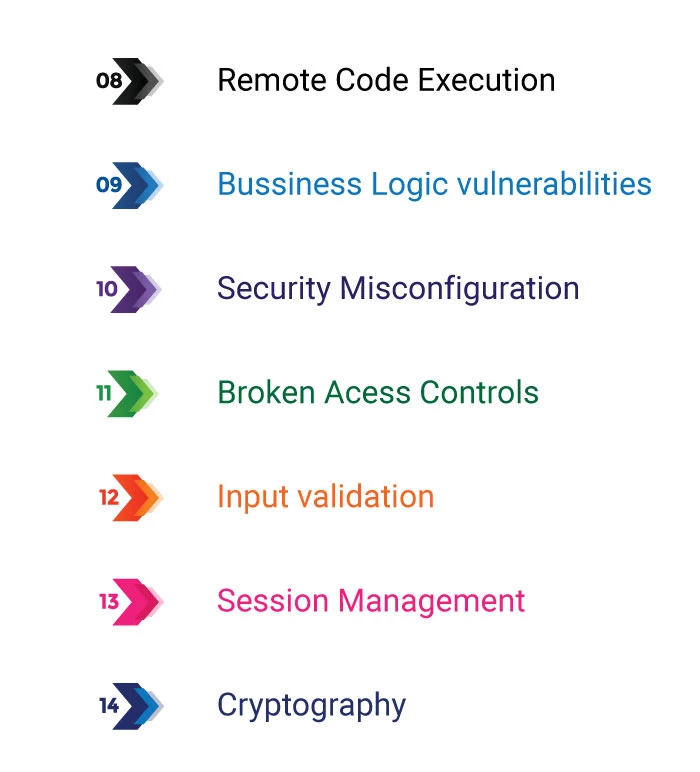
Our Application Penetration Testing focuses on 14 critical risks
Our primary objective for a web application penetration test is to identify exploitable vulnerabilities in applications before hackers are able to discover and exploit them. Web application penetration testing will reveal real-world opportunities for hackers to be able to compromise applications in such a way that allows for unauthorized access to sensitive data or even take-over systems for malicious/non-business purposes. These tests seek to identify expected functionality, reliability, performance, and security. To identify critical application-centric vulnerabilities, our testers will first look to gather information about the app and its environment. Next, they will model threats, analyze vulnerabilities, and work to exploit those vulnerabilities. After determining what happens post-exploitation, the testers will provide clear, comprehensive reporting that helps you prioritize the next steps for remediation.









Methodology We Practice
Our unique way of procedures for a seamless delivery of end results
1. Passive Reconnaissance
We focus on collecting as much information as possible about the target, through analysis, it begins by understanding the attack surface and its primary operations,such as API calls.
2. Modelling of Threats
The modelling of Vulnerabilities, exit points, entrance points, cameras, guards, fences, company technology, staff members and other relevant information are used to begin planning an attack.
3. Analysis of Vulnerability
During these phases, Our team carries out the plan by Analyzing the vulnerabilities using information and intelligence captured during the earlier phases of the assessment.
4. Exploitation Of the Vulnerability
In this stage we identify Security flaws present in the environment by conducting both automated & manual testing in the view of a hacker and an experienced security professional.
5. Post exploitation
Post-exploitation involves penetrating further into the environment and setting up to maintain a persistent backdoor.This depends on the client scope of testing and opinion based on their environment setup.
6. Reporting
A details exclusive report on the vulnerabilities found during the previous phases are mentioned in the properly formated document which can be understood by the developer for the remediation.
What all can
be tested ?
API testing
As APIs increasingly connect our most intimate and sensitive data they rise in value. Today’s applications might expose hundreds of highly valuable endpoints that are very appealing to hackers. Ensuring your APIs are secure before, during, and after production is becoming table stakes.
Web Application
A client–server computer program that the client runs in a web browser. Common web applications include webmail, online retail sales, online banking, and online auction, E-Commerce which are the most targeted scopes in the recent times which are covered by our service.
Mobile Application
The rapid development in the mobile sector also lead to increment in the attack surface for the hackers, so the firmware based attacks and Man in the Middle attacks are such example that are tested by us at the primary stage of testing.
Thick Clients
A client in client–server architecture or network and typically providing rich functionality, independent of the server is tested for Vulnerabilities such as Improper Error handling , XSS , Denial Of service , Parameter tampering, Clickjacking , Sql Injections.
Frequently asked common questions
Why cyber security is important, and why many organizations and agencies globally choose team of professionals from Defmax.
- Why do I need a VAPT?
- VAPT, aka Penetration Testing, is a must needed process for any organization these days due to raise in large number of hacking attempts everywhere. Attacks are being happen from internally or externally of the organization assets. It helps in identifying higher-risk vulnerabilities, security weakness and also test security policy compliance of your organization.
- Who will be doing security test?
- Our internal team of industry standard certified security analysts and professionals experienced in your applications platform will carry tests on your assets. We detail every vulnerability and make sure quality standards are met.
- How frequently Penetration Testing needs to be done?
- Penetration Testing on any applications of web/mobile has to be performed regularly based on code changes, team changes or compliance and regulatory requirements. Some organizations carry out the activity twice a year while some go as far as on a daily, monthly or quarterly basis.