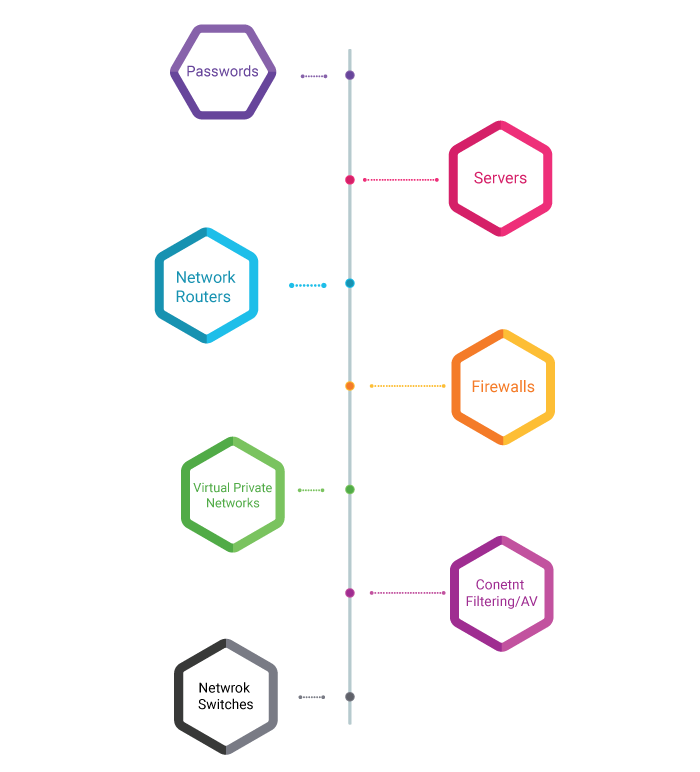
What Network Penetration Testing Covers
Network penetration testing will reveal real-world opportunities for hackers to be able to compromise systems and networks in such a way that allows for unauthorized access to sensitive data or even take-over systems for malicious/non-business purposes. Our penetration attempting out technique includes an attack simulation done through our rather skilled safety experts on the way to:
- Identify Security flaws within the environment
- Understand the extent of damage on your enterprise
- Help address and attach diagnosed network security flaws








